Last week @jarwidmark and myself held a live session about windows 10 deployment notes from the field and we had ALOT of good questions.
Here are the questions and answers from the session
Q: How well does the performance of an NVMe drive compare to an M2 SSD?
A: There are both M2 NVMe and M2 SSD drives available at the current time. However, the NVMe drives are a different type of drives even if they are connected using the slot type. NVMe will always be faster but depending on what you need to do it might not be economical.
Q: Can Secure Boot be disabled and enabled after Windows 10 installation?
A: Yes, Secure Boot can be disabled/enabled after Windows installation. Note that turning UEFI on/off is not the same thing!
Q: Is peercache similar to a product such as 1E Nomad?
A: Yes, peerchache is very similar to those types of products. What you need to remember is that peercache has now been around for all of 2 months while products similar third party products have been out for a couple of years. There is a good write up about this topic made by 2Pint Software found here https://2pintsoftware.com/peer-cache-in-configmgr-current-branch-first-impressions/
Q: What’s the best way to upgrade from Windows 7 to Windows 10 1607 in place?
A: As of right now the best way is using the Replace scenario so backup the current computer and redeploy it as a new computer while restoring the settings and documents. This will enable you to turn on UEFI+SecureBoot and any other new features you desire.
If you do a normal in-place upgrade there is currently no way of switching from Legacy BIOS to UEFI and thus you will not be able to use all the new cool features of Windows 10.
Q: how do you prevent Windows 10 from automatically uninstalling software it deems “not compatible” when doing Windows update? Example: Cisco VPN client app, when updating versions (i.e. 1507->1511)
A: Don’t use Windows Update, use sequencing instead. Either with MDT or SCCM. That way you can control before, during and after. Giving you the tools you need to get the job done. In this case making sure the software is reinstalled or upgrade as part of the in-place upgrade.
A good starting point can be found here http://deploymentresearch.com/Research/Post/533/Improving-the-ConfigMgr-Inplace-Upgrade-Task-Sequence
Q: For the in-place upgrade Task Sequence, is it possible to add Cumulative Update to the image rather than adding the CU to the TS? Running a Cumulative Update during the TS adds a lot of time to the deployment.
A: Yes, you can add both CUs and Security fixes to a install.wim file. That is fully supported. However, as it will use offline servicing to do so the patches won’t be installed until the machine is booted up and during the initial boot they will install. This will take the same amount of time as adding them as applications during the TS.
Q: Which OSs are supported by MDT 8443?
A: Windows 7 and forward. Note that MDT 8443 requires ADK1607 and that ADK has issues with Windows 7 and driver injection when running on SSD drives.
Q: Is the best way to customize default pinned apps in the Win 10 task bar still via a run-once logon script?
A: No, use the start and taskbar layout xml file instead. More info on that can be found here https://technet.microsoft.com/en-us/itpro/windows/manage/windows-10-start-layout-options-and-policies
Note that taskbar pinning using xml requires Windows 10 1607.
Q: Have you seen any new hardware components with no Win7 drivers?
A: Yes, not all new models support Windows 7. This is due to instruction sets in some of the Skylake CPUs by Intel. Most vendors have a number of models/configurations that do support Windows 7 still. Expect this to diminish now that Kaby Lake is out and going forward with new CPUs.
Q: With Win 7/8.1 we would use Copyprofile, configure items in the captured image, and that worked great. Since Copyprofile is a no-go with Win10 it seems, what is the best approach going forward? WICD? Don’t configure in captured image, but apply during deployment TS?
A: Microsoft is moving towards less IT configuration and more personal configuration by end-users. This makes it less worthwhile doing customizations but when you need to do them you have a couple of options. Do the in the deployment TS or use GPOs. Since in-place upgrade is going to be the way between versions and you can’t customize the install.wim file moving them elsewhere will be needed.
Q: Is it better to remove Appx packages from win 10 via a powershell script during OS deployment, or via applocker (so that they never get installed for the users) anyone have experience/comparison to both
A: Removing Appx packages can only be done with PowerShell. Applocker will not remove them only block them from being used. If you want to scale down on the apps make sure to remove AppX packages and the AppX provisioned packages.
Q: Why don’t use ConfigMgr for reference images?
A: Until very recently that was not an option due to the fact that ConfigMgr will install the client as part of deployment and we want to avoid that. We still prefer MDT due to the fact its smaller, needs to infrastructure to work, its much faster and you also get a profile that can be customized to some extent.
Q: In your experience, has anyone needed hardware upgrades to go from win7 to win10? Or are real-world HW requirements the same?
A: This is a split question. If a model is supported no they won’t need an upgrade x64 requirements for Windows 7 and 10 are the same. Windows 10 will even be kinder to your hardware giving you more bang for your buck.
The thing to lock out for is of course that old models might not be vendor supported for Windows 10 and a lot of older models does not support full UEFI. Thus, for those models you won’t be able to turn on features like, Device guard and Credential guard.
Q: Would MDT Version: 6.2.5019.0 work with Win 1607, if I was to start testing deployment?
A: No, you will need a newer ADK and that is not supported with the old versions of MDT. The newer version of MDT also contains a massive amount of bugfixes so make sure to upgrade MDT instead.
Q: Does CM1610 with MDT 8443 support ADK 1511? I ask because we have to use 802.1x port authentication in our boot images and that is broken in ADK 1607.
A: Kind of, 1606 does support ADK1511 and I have not seen statements that 1610 requires ADK1607 to work. Its more a question on which OS you want to deploy. Check the link for support statement on ADK and ConfigMgr from the Microsoft Team.
https://blogs.technet.microsoft.com/enterprisemobility/2016/09/09/configuration-manager-and-the-windows-adk-for-windows-10-version-1607/
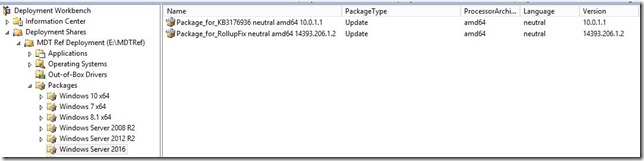
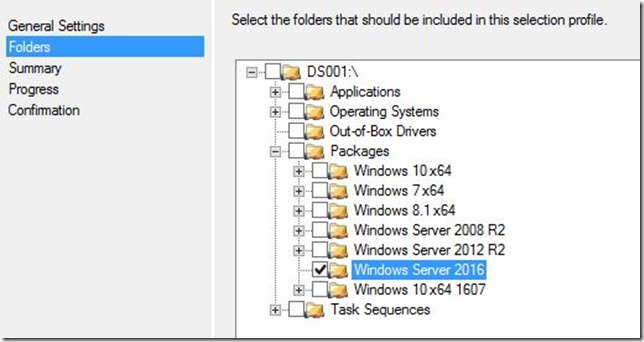
Q: What was the package to add for Win 10 v1607 in MDT to fix WU issue?
A: Make sure to add the latest CU for November that is KB 3200970 http://support.microsoft.com/?kbid=3200970 together with servicing stack update KB3199986 https://support.microsoft.com/en-us/kb/3199986
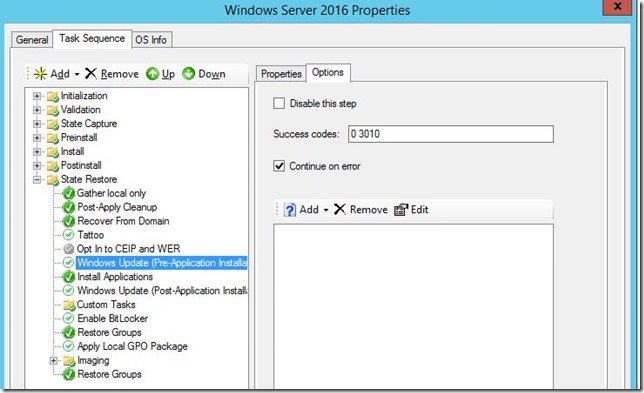
Q: Adding the CU via a Package, but it still appears to download it from WU. Also, tried to add it the image via DISM, but same result. Any suggestions on how to prevent it from downloading?
A: This is a known issue that can be read from the KB article. To avoid it install them as applications before the first Windows Update step runs.
Q: KB3197954 is superseded so just add in the next Cumulative Update for Windows 10 Version 1607? do the next one have a working WU agent or do a first need to install this one?
A: No, all CUs contains all the previous month’s patches so the latest one will cover everything you need.
Q: What could we expect roadmap wise, with MDT and SCCM, compared to roadmap of Win 10? Will MDT / SCCM keep up?
A: Both ConfigMgr and MDT is dedicated to staying current with Windows 10. This means that MDT will be updates when needed for deployment and ConfigMgr will get continues releases to add features and fix bugs. Just this year we have seen 3 production releases of ConfigMgr (1602, 1606 and 1610)
Q: What’s the top benefits using MDT+ConfigMgr together?
A: MDT adds about 280 built-in features through scripts. You may of course build that yourself using native ConfigMgr but I have more fun things to do with my time. And if you build them yourself you will have to support them. MDT on the other hand is supported by Microsoft.
Q: Do you recommend custom Windows10 images and what is your go to image creation tool?
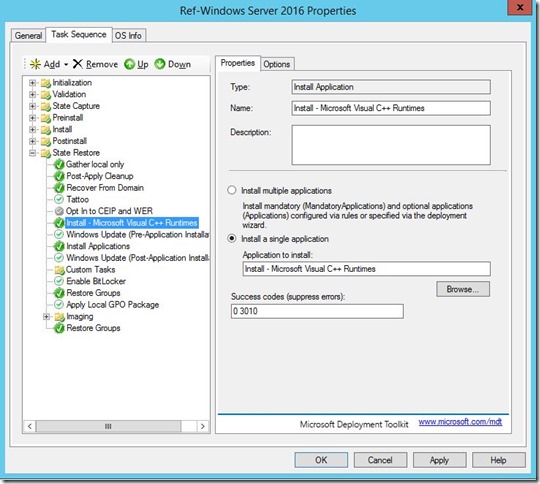
A: Always use MDT for reference image creation. I recommend using custom images for bare metal deployment so you can add in things your end users will need, like Visual C++ runtimes and .Net Framework. For upgrades, custom images are not supported so you will need both.
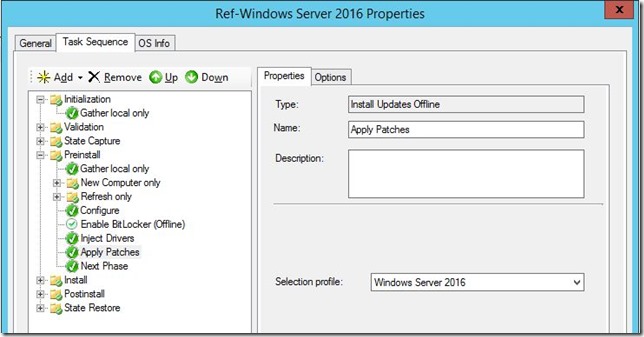
Q: When creating a W10 ref image, would you recommend applying the latest CU offline or online?
A: Both work but if you want to save time do them online otherwise it will redownload the patch to apply certain things again.
Q: Deploying with 1607 ADK working with win 7 deployment?
A: There is one big issue using the ADK 1607. Driver injection on Windows 7 with ADK1607 will fail when running on SSD drives. Using a ADK1511 boot image will solve that issue.
Hope this has helped you out with your deployments
/Peter